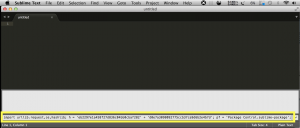
Open Sublime Text 3 console using shortcut: ctrl+` and then paste the below code following by Enter:
import urllib.request,os,hashlib; h = 'eb2297e1a458f27d836c04bb0cbaf282' + 'd0e7a3098092775ccb37ca9d6b2e4b7d'; pf = 'Package Control.sublime-package'; ipp = sublime.installed_packages_path(); urllib.request.install_opener( urllib.request.build_opener( urllib.request.ProxyHandler()) ); by = urllib.request.urlopen( 'http://packagecontrol.io/' + pf.replace(' ', '%20')).read(); dh = hashlib.sha256(by).hexdigest(); print('Error validating download (got %s instead of %s), please try manual install' % (dh, h)) if dh != h else open(os.path.join( ipp, pf), 'wb' ).write(by)
See also code in Sublime Text Console window:
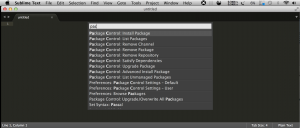
Then tap Shift+Cmd+p and type “package control: install package”, select and press the Enter key:
in the textarea type in “NASM x86 Assembly” select the first (and one) from list result to add the package:

Last, open your assembly file and Sublime Text 3 menu, select View | Syntax | Assembly (x86) NASM and enjoy the colored syntax.